How to Use Proxy Like a Pro

Using a proxy is no longer a technique reserved for IT professionals or cybersecurity experts. From businesses managing multiple accounts to individuals protecting their privacy, proxies have become essential tools in the digital age. However, simply turning on a proxy server is not enough to maximize its benefits. To truly use a proxy like a professional, one must understand how it works, when to apply different types, and how to optimize performance while maintaining security.
TLDR: Proxies act as intermediaries between users and the internet, enhancing privacy, security, and access control. To use them like a pro, one must choose the right type of proxy, configure it correctly, rotate IPs strategically, and monitor performance. Proper security practices and ethical usage are essential. Mastery comes from combining technical setup with strategic intent.
What Is a Proxy and How Does It Work?
A proxy server acts as an intermediary between a user’s device and the internet. Instead of connecting directly to a website, requests pass through a proxy server, which then communicates with the destination site on the user’s behalf. The website sees the proxy’s IP address rather than the user’s actual IP.

This simple switch adds layers of functionality, including:
- IP masking for increased anonymity
- Geo-location changes to access region-restricted content
- Traffic filtering for corporate or parental control
- Load distribution for business operations
Professionals understand that a proxy is not merely about hiding identity. It is about controlling digital presence and managing online interactions strategically.
Types of Proxies and When to Use Them
Knowing the difference between proxy types is crucial. Each serves a distinct purpose, and selecting the wrong one can lead to poor performance or security risks.
1. Residential Proxies
These use real IP addresses assigned by Internet Service Providers. They are ideal for tasks requiring high trust levels, such as:
- Social media management
- E-commerce price monitoring
- Ad verification
Because residential IPs appear authentic, they are less likely to be blocked.
2. Datacenter Proxies
These originate from cloud hosting services rather than ISPs. They are:
- Faster
- More affordable
- Suitable for bulk data tasks
However, they may be easier for websites to detect and block.
3. Mobile Proxies
Mobile proxies use IP addresses assigned by mobile carriers. They provide extremely high trust scores because multiple users share mobile IP pools. These are best for:
- App testing
- Mobile ad verification
- Managing mobile-first platforms
4. Rotating vs. Static Proxies
Rotating proxies automatically change IP addresses at intervals, reducing detection risks. Static proxies maintain the same IP address, useful for account consistency and login stability.
A professional chooses based on the goal rather than defaulting to a single solution.
Setting Up a Proxy Like a Professional
Configuration separates amateurs from experts. Proper setup depends on the application—browser use, system-wide configuration, or integration into specific tools.
Browser Configuration
Most browsers allow manual proxy settings. Professionals ensure:
- Correct IP address and port entry
- Authentication credentials are securely stored
- HTTPS support is enabled
Testing with an IP-checking website confirms whether the proxy is active.
System-Wide Setup
Configuring proxies at the operating system level routes all traffic through the proxy. This is common for:
- Business environments
- Security-focused users
- Automation setups
Using Proxy Managers
Advanced users rely on proxy management software to:
- Rotate IP addresses automatically
- Manage multiple proxy pools
- Track performance metrics
This level of control allows seamless scaling of operations.
Advanced Strategies for Pro-Level Proxy Usage
IP Rotation Tactics
Rotating too frequently can appear suspicious, while rotating too slowly increases block risk. Professionals synchronize rotation intervals with task type:
- Short sessions for data scraping
- Longer sessions for social media accounts
User Agent Matching
IP changes should align with browser fingerprints. Mismatched user agents can trigger detection systems. A residential IP paired with a realistic browser profile maintains authenticity.
Geo-Targeting With Precision
Instead of broadly selecting a country, professionals narrow targeting to specific cities or regions when verifying ads or localized search results.
Bandwidth Monitoring
High-traffic operations require tracking bandwidth usage. Exceeding quota limits can interrupt campaigns or automation processes. Monitoring dashboards help maintain cost efficiency.
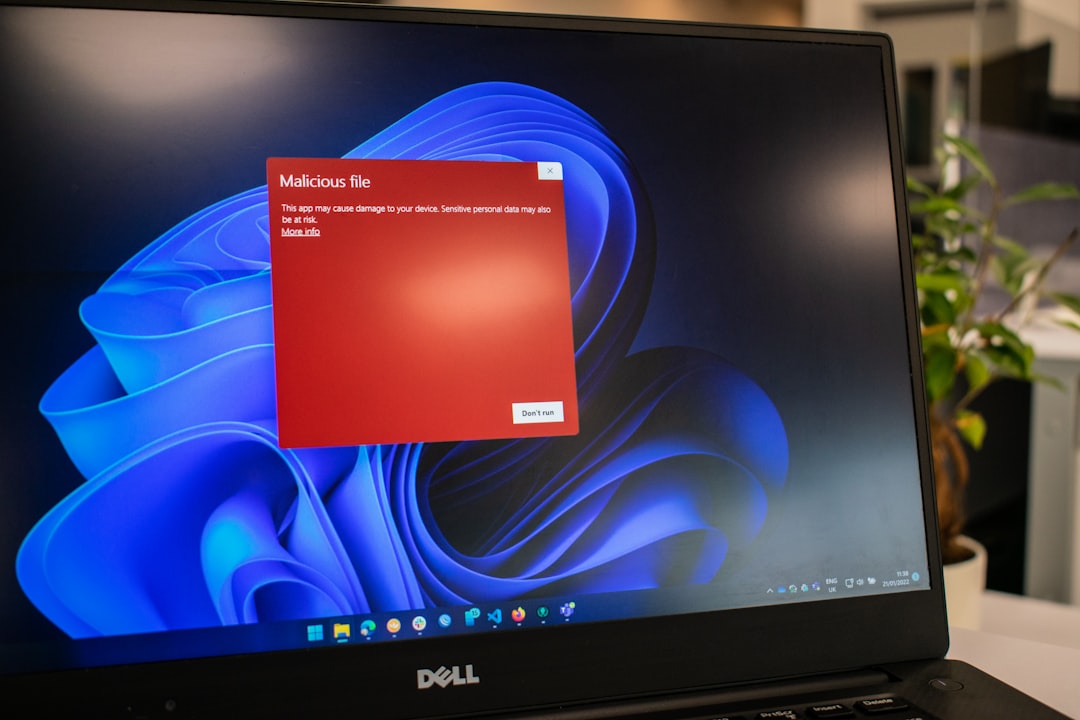
Security Best Practices
A proxy enhances privacy, but improper usage can introduce vulnerabilities.
- Always use HTTPS proxies to encrypt traffic
- Avoid free proxy lists, as they may log data or inject malware
- Update authentication credentials regularly
- Combine proxies with VPNs cautiously to avoid connection conflicts
Professionals also review provider logging policies. A truly privacy-focused proxy service should have transparent data handling practices.
Common Mistakes to Avoid
Overloading a Single IP
Sending excessive requests through one proxy can lead to bans. Load distribution is key.
Ignoring Website Terms of Service
Ethical usage protects both reputation and operational continuity. Violating platform rules can result in account suspension.
Neglecting Speed Testing
Latency issues slow down workflows. Professionals test multiple servers and select those with the lowest ping and fastest response times.
Failing to Backup Proxy Pools
Having alternative IP pools ensures uninterrupted service if a provider experiences downtime.
Business Applications of Professional Proxy Use
Companies leverage proxies in highly strategic ways:
- Market Research: Monitoring competitors across regions
- Cybersecurity Testing: Simulating attacks from different IP ranges
- Brand Protection: Identifying counterfeit listings
- Data Aggregation: Collecting public web data responsibly
The professional mindset focuses on operational efficiency, risk management, and long-term sustainability.
Measuring Proxy Performance
Experts continuously evaluate:
- Response time
- Success rate
- Block frequency
- Cost per gigabyte
Analytics tools help determine whether a proxy setup remains viable or requires adjustment.
The Ethical Dimension of Proxy Use
Using a proxy like a professional includes respecting legal boundaries. Proxies should not be tools for fraud, harassment, or unauthorized access. Ethical use ensures that privacy, research, and security remain the core objectives.
A responsible user evaluates the legal framework within their jurisdiction and complies with applicable data and cybersecurity laws.
Conclusion
Mastering proxies involves more than technical configuration. It requires selecting the correct type, optimizing rotation strategy, maintaining security standards, and continually analyzing performance. Professionals treat proxies as strategic assets rather than quick fixes. With the right approach, proxies become powerful tools for privacy management, market intelligence, and operational scalability.
FAQ
- What is the main purpose of a proxy?
A proxy primarily acts as an intermediary between a user and the internet, masking the user’s IP address and providing added privacy, security, or access control. - Are proxies legal to use?
In most countries, proxies are legal. However, how they are used determines legality. Engaging in illegal activities through a proxy remains unlawful. - What is the difference between a proxy and a VPN?
A proxy typically reroutes specific traffic, while a VPN encrypts and routes all internet traffic through a secure tunnel. VPNs provide broader encryption. - Do free proxies work well?
Free proxies often lack reliability, speed, and security. They may log user data or expose users to malware. Paid services are generally safer and more stable. - How often should IPs rotate?
Rotation frequency depends on the task. Data scraping may require frequent rotation, while account management benefits from longer, stable sessions. - Can proxies improve internet speed?
In some cases, caching proxies can improve speed. However, many proxies slightly reduce speed due to the additional routing step.
